k3s的安装
curl -sfL https://get.k3s.io | sh -s -简单部署deployment 和service
创建文件: xxx-deployment.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: xxx
spec:
replicas: 1
selector:
matchLabels:
app: xxx
template:
metadata:
labels:
app: xxx
spec:
containers:
- name: bibleplan
image: franklinxia/xxx:1
ports:
- containerPort: 8285
args: ["--spring.config.location=/opta/xx/application.yml"]
volumeMounts:
- name: config-volume
mountPath: /opta/xxx
#subPath: application.yml
readOnly: true
volumes:
- name: config-volume
hostPath:
path: /opt/zhunei/k3s/xxx
type: Directory
---
apiVersion: v1
kind: Service
metadata:
name: xxx
spec:
selector:
app: xxx
ports:
- protocol: TCP
port: 80
targetPort: 8285使用命令查看是否成功:
kubectl get deployment
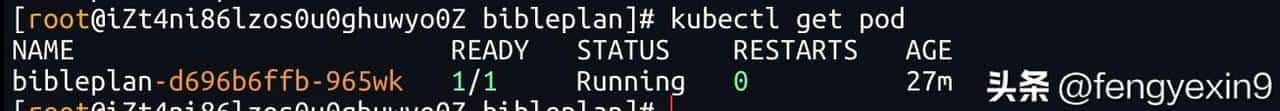
kubectl get podkubectl get pod
kubectl logs -f bibleplan-d6… 查看是否运行正常;
要是删除 该pod
可以使用:
kubectl delete deployment xxx
kubectl delete service xxx或者
kubectl delete -f xxx-deployment.yaml开启证书:
安装 cert-manager(一次性)
kubectl apply -f https://github.com/cert-manager/cert-manager/releases/download/v1.14.4/cert-manager.yaml创建 Let’s Encrypt 颁发器(ClusterIssuer)
创建
letsencrypt-clusterissuer.yaml
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata:
name: letsencrypt-prod
spec:
acme:
email: xxx@qq.com # ⚠️ 换成你自己的
server: https://acme-v02.api.letsencrypt.org/directory
privateKeySecretRef:
name: letsencrypt-prod
solvers:
- http01:
ingress:
class: traefik执行: letsencrypt-clusterissuer.yaml
kubectl apply -f letsencrypt-clusterissuer.yaml执行kubectl get clusterissuer,下面执行结果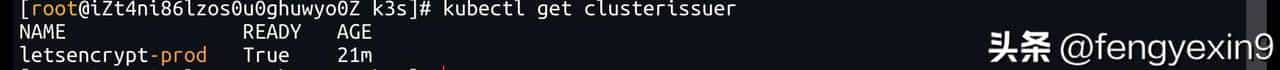
下面在配置ingress
创建xxx-ingress.yaml (下面的支持可以访问http和https)
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: biblesystem-ingress
annotations:
# kubernetes.io/ingress.class: "traefik"
# cert-manager.io/cluster-issuer: letsencrypt-prod
# kubernetes.io/ingress.class: traefik
cert-manager.io/cluster-issuer: letsencrypt-prod
traefik.ingress.kubernetes.io/router.entrypoints: web,websecure
traefik.ingress.kubernetes.io/redirect-entry-point: websecure
# traefik.ingress.kubernetes.io/router.tls: "true"
spec:
ingressClassName: traefik
tls:
- hosts:
- sys.ii.com
secretName: tls-app-a
rules:
- host: sys.ii.com
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: xxx #servuce的名字
port:
number: 80执行命令如下:
kubectl apply -f xxx-ingress.yaml执行后访问http和https域名;
kubectl get ingress
kubectl delete -f xxx-ingress.yaml© 版权声明
文章版权归作者所有,未经允许请勿转载。













查看证书: kubectl get pods -n cert-manager