稿件来源:CQ现代通信
天线是所有具备无线通信功能的设备的关键换能器件,用来发射和接收电磁波信号,可以说是电磁波进出无线电台的门户。它接收电磁波,转换成电流,也把电波转换成电磁波辐射出去。它的作用有点像是音响系统里的喇叭和话筒。
对于无线电台来说,天线具有特别重大的作用,一个性能良好的无线电收发系统,必须配备性能良好的天馈线系统才能充分发挥其作用。甚至有人说“有好机器不如有好天线,有好天线不如有好的传播”,足可见天线系统在整个电台系统中的重大性。
天线的工作原理
天线在发射的时候大致是这样的:在导线中有高频交变电流流动就会在导线的周围激发出电磁波,形成的电磁波以光速向外辐射。这样,导线就实现了天线的功能,这段导线也就成为了天线的振子。
天线接收的过程与发射相反。
天线长度与波长的关系
为了提高天线辐射电磁波的强度,必须使流过天线导体的高频电流尽量的强。我们知道当电路处于谐振状态下时,电路中的电流最大。因此,天线处于谐振状态时天线的辐射最强。
由传输线理论可知,当导体长度为1/4波长的整数倍时,该导体在该波长的频率上呈谐振特性。导体长度为1/4波长时为串联谐振特性,而导体长度是1/2波长呈并联谐振特性。由于1/2波长的振子比1/4波长的振子长,所以,1/2波长振子的辐射会比1/4波长振子强。
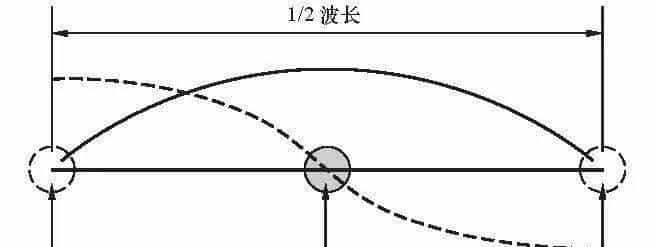
图中为半个波长示意,可以看到1/4波长处电流最强
振子超过1/2波长虽然辐射会继续加强,但由于超过1/2波长部分的辐射呈反相位,其对辐射有抵消的作用,因而总的辐射效果反而被打折扣。所以,一般的天线都是采用1/4波长或者1/2波长的振子长度单位,这种由两根一样长度导体振子构成的天线就构成所谓的偶极子天线。其中实用性最强的是半波长振子偶极天线,这种天线从中心馈电,两边各接1/4波长的导电体振子,构成的天线左右对称。这是最简单、最基本的天线,其他的许多天线形式都可以等效成偶极子天线的变形和叠加。
同样结构的天线,工作频率越低,波长就越长,则天线的振子也需要越长,天线也就显得越庞大,短波天线因此一般都显得比V/UHF的天线要庞大和雄伟。

庞大的短波天线阵
缩短系数
大家都知道电波在真空中以每秒钟30万公里的光速传播,但在不同的介质中会有不同的传播速度,其波长也会改变。因而,在不同的介质里,天线的谐振振子长度可以缩小,这就是缩短系数。
例如在空气中的缩短系数是0.98。有的介质其缩短系数很大,可以使天线大大地缩小。但一般在介质里电波的损耗比真空或空气要大许多,因而这样的天线效率并不高。
收发互易特性
天线具有收发互易的特性,天线在接收时的许多特性和参数都可以由该天线在发射状态时的已知特性及参数决定,反之亦然。简单地说若一条天线的接收效果好,则该天线的发射效果也好。
但是,当通过电离层反射进行长距离短波发射和接收时,由于接收到的和发射出去的电波其传输途径并不总是完全一样,就会出现天线的接收和发射可能并不完全互易的情况。
总的来说,一个好的天线系统,第一是天线系统本身的辐射效率要高,自身的损耗要小,其次是要能与传输系统相匹配,使整个收发天馈系统的传输效率达到最高,再次就是能尽量地使所辐射的能量都聚焦到所需要的地方,抑制不必要的辐射。
本文节选自《现代通信》杂志,作者吴国光(BA7IA),转载请注明出处:《现代通信》杂志公众号【CQ现代通信】。
现代通信,中国火腿自己的杂志。














收藏了,感谢分享